resource
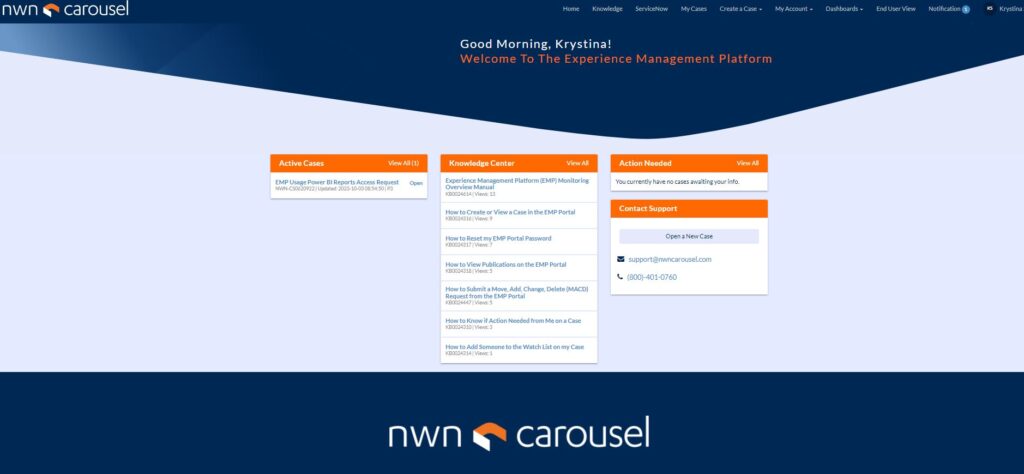
Experience Management Platform
NWN Carousel’s Experience Management Platform (EMP) unifies the people, processes, and technology required to operate, optimize, and transform your cloud & on-prem ecosystems.
EMP is comprised of two integrated components:
- EMP Services: Managed Services delivered to support our six core integrated offers. Providing a cost-effective way to manage IT environments.
- EMP Customer Portal: A role-based platform granting users control over the entire customer journey.
Want unified management of your multi-cloud environment?
Become EMPowered.
EMP enhances the business user experience by centralizing information into a single source of truth across integrated technologies, enabling customers to maximize investments & reduce complexity.
- Visibility: Aggregate visibility into environments and services
- Control: Manage solutions through administration and self-care capabilities
- Analytics and reporting: Increase insights and maximize investment
- 24×7 Support: Communicate directly with NWN Carousel experts via a secure platform
Learn how EMP delivers a unified view into your environment – from core to cloud!
“Our partnership with NWN Carousel during the pandemic enabled us to quickly pivot to a work-from-home model. We came up with a solution where we were imaging desktops at a remote location and drop-shipping them by the hundreds to our at-home agents. This allowed us to continue to serve our over 4 million customers.
We also gained critical visibility into our ticketing, reporting and full IT networking environment with NWN Carousel’s Experience Management Platform.”
Carmine Buffa
Director, IT, HomeServe
Experience Management Platform (EMP) enhances the user experience by centralizing information into a single source of truth
Visibility into multi-tenant environments and services
Manage solutions through administration and self-care
Deeper, richer insights to maximize your investment returns
Communicate directly with experts via an secure always-on platform
Download the Solution Brief
NWN Carousel’s EMP enhances the user experience (UX) by centralizing information into a single source of truth across integrated technologies, enabling customers to maximize technology investments and reduce complexity. NWN Carousel delivers the EMP in a SaaS model via public, private, and hybrid cloud, removing the need for organizations to manage any on-premise communications infrastructure.

Resources
Wait…checkout these perfect pairings to EMP →
Unified Communications (UCaaS)
Embrace true mobility for a seamless transition between work styles. NWN provides core unified communications and next-gen collaboration capabilities as an integrated solution/offering that is simple to consume, use and manage for organizations of all sizes. Taking on the complexity on our customer’s behalf.
Contact Center
The provision of quality customer service is essential to the successful operation of a contact center. The quality of the exchange between an operator and a customer can be greatly enhanced by a well-constructed, implemented, and communicated plan.

Be EMPowered
Watch a recorded episode and learn how our Experience Management Platform offers advanced analytics, real-time reporting, service desk capabilities, and proactive alerts as a single source of truth.